10 March 2026
Report Says iPhone-Hacking Toolkit Used by Russian Spies Likely Originated With U.S. Military Contractor.
Brief summary
All images are AI-generated. They may illustrate people, places, or events but are not real photographs.
Press the play button in the top right corner to listen to the article

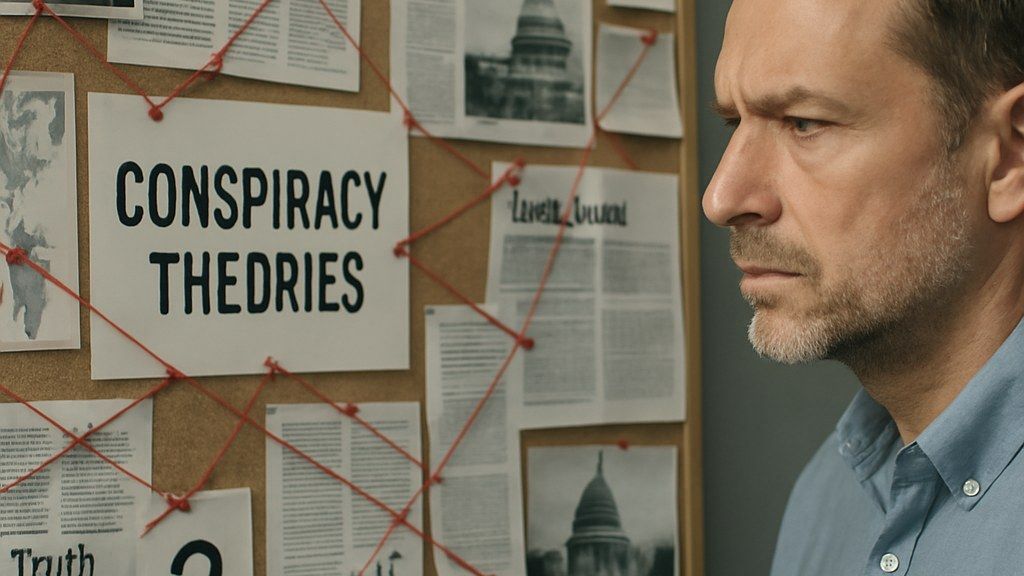
A technical report released Tuesday said an iPhone-hacking toolkit linked to Russian intelligence activity likely originated from a U.S. military contractor, raising new questions about how advanced cyber capabilities can spread beyond their original developers and into foreign espionage operations.
A newly released technical assessment has concluded that an iPhone-hacking toolkit used in operations attributed to Russian spies likely came from a U.S. military contractor, according to details published Tuesday.The report describes a set of tools designed to compromise Apple’s iPhone devices and support follow-on access. It links the toolkit to activity associated with Russian intelligence operators and says the most plausible origin points to a U.S.-based contractor that works on military-related programs.
The assessment does not publicly identify the contractor by name. It also does not provide a definitive account of how the toolkit moved from its apparent point of origin into the hands of Russian operators. Instead, it frames the conclusion as a likelihood based on technical indicators and similarities between the toolkit and other known development patterns.
The findings arrive amid continuing scrutiny of the global market for offensive cyber tools, including the risks posed when sophisticated capabilities are reused, repackaged, or obtained by actors other than the original customer. The report’s focus on iPhone exploitation underscores the value of mobile-device access for intelligence collection, given the volume of personal and professional communications that pass through smartphones.
## Findings and attribution
According to the report, analysts examined code-level and operational characteristics of the iPhone-hacking toolkit and compared them with other tools and techniques previously documented in the cyber domain. The assessment says the toolkit’s design and implementation suggest it was developed with significant resources and expertise.
The report ties observed use of the toolkit to Russian espionage activity. It characterizes the operators as Russian spies and describes the toolkit as having been used in campaigns targeting iPhone devices. The report does not provide victim counts or a geographic breakdown in the information released Tuesday.
The assessment’s central claim is that the toolkit likely originated with a U.S. military contractor. The report presents this as an analytical judgment rather than a confirmed chain of custody. It indicates that the conclusion is based on technical signals that point to a development environment and practices consistent with contractor-built offensive tooling.
The report does not state whether the toolkit was taken through theft, unauthorized transfer, resale, or other means. It also does not specify whether the contractor was aware of any compromise or loss of tools.
## Implications for contractors and government oversight
The report’s conclusion highlights a recurring governance challenge for governments and defense contractors: controlling access to sensitive cyber capabilities and preventing their proliferation.
Military contractors often develop software and technical systems under government contracts, including tools used for testing, intelligence support, and other security-related missions. When offensive cyber tools or components are exposed outside intended channels, they can be repurposed by foreign intelligence services or criminal groups.
The report does not allege wrongdoing by any specific company or government entity. However, its findings are likely to intensify attention on how contractors secure code repositories, development systems, and operational tooling, and how governments monitor the lifecycle of cyber capabilities created under contract.
The assessment also underscores the difficulty of attribution and provenance in cyber incidents. Even when analysts can link a toolkit to a particular operator, determining where the code originated and how it changed hands can be more complex, especially when tools are modified, shared, or rebuilt over time.
## Mobile exploitation and the iPhone security landscape
The report centers on iPhone hacking, reflecting the strategic value of mobile-device access for intelligence operations. Smartphones can provide access to messages, call records, location data, photos, and authentication tokens, depending on the level of compromise.
The assessment does not detail the specific vulnerabilities or exploitation methods used by the toolkit in the information released Tuesday. It also does not state whether the techniques remain effective against current iPhone software versions.
Apple has repeatedly emphasized security updates and device hardening over time, and iPhone exploitation typically depends on identifying and using software weaknesses before they are patched. The report does not indicate whether the toolkit relied on previously unknown vulnerabilities or on known issues that were not yet fixed at the time of use.
The report’s broader point is that advanced mobile exploitation capabilities can circulate beyond their original developers. That circulation can complicate defensive efforts, because the same or similar techniques may appear in multiple campaigns and be used by different actors.
The report released Tuesday does not announce any enforcement action, sanctions, or formal government investigation. It presents its findings as a technical assessment intended to document the toolkit, its use, and the likely origin of its development.
The publication date of the report coincides with renewed debate in multiple countries over how offensive cyber tools should be governed, including questions about contractor accountability, security standards for sensitive development work, and the risks of tool proliferation in an increasingly contested digital environment.
AI Perspective
41
The content, including articles, medical topics, and photographs, has been created exclusively using artificial intelligence (AI). While efforts are made for accuracy and relevance, we do not guarantee the completeness, timeliness, or validity of the content and assume no responsibility for any inaccuracies or omissions. Use of the content is at the user's own risk and is intended exclusively for informational purposes.
#botnews