[[[SUMMARY_START]]]
Cyber threats are no longer limited to giant data breaches or attacks on big companies. Increasingly, criminals are using texts, email, social media and fake websites to trick ordinary people into giving up money, passwords and personal data.
Recent official data and security reports show that phishing, text scams, account takeovers and infostealer malware are growing threats. The shift means daily habits on phones and laptops now sit at the center of personal cybersecurity.
[[[SUMMARY_END]]]
For years, public attention around cybersecurity focused on dramatic events: major ransomware attacks, giant data leaks and corporate hacks. Those threats still matter. But the day-to-day danger for many people now looks much smaller, more personal and often much more ordinary.
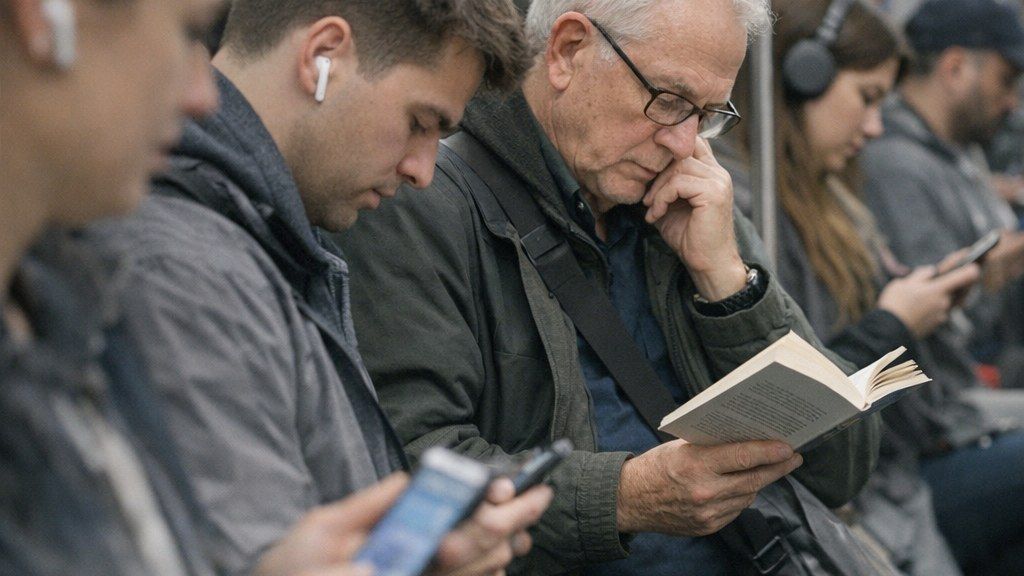
A fake toll text. A package delivery warning. A message that appears to come from a bank, an employer or a family member. A login page that looks real. A call that sounds urgent and familiar. Modern cybercrime is increasingly built around these moments, using trust, speed and confusion to target regular people where they spend most of their time: on phones, in inboxes and inside apps.
The broad trend is clear. Criminals are not relying only on rare, technically complex intrusions. They are also using low-cost, repeatable scams that can be sent to huge numbers of people in seconds. That makes everyday users a direct target, not just collateral damage from a breach at a large company.
The latest annual figures from the FBI’s Internet Crime Complaint Center showed 859,532 complaints in 2024, with reported losses above $16 billion. That was a sharp rise from the year before. The numbers cover many forms of online crime, but together they show how large the financial impact has become for households, workers and small organizations.
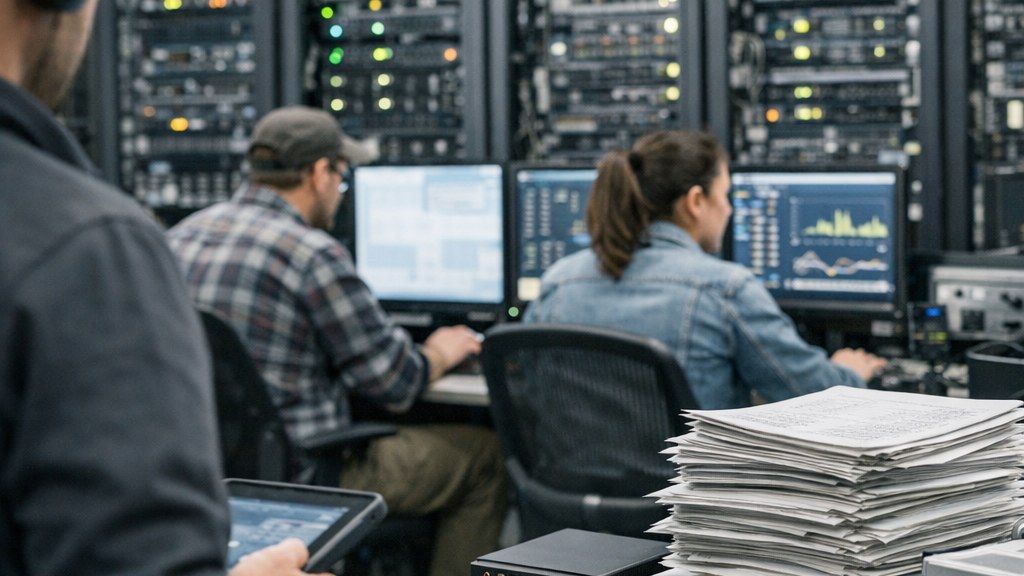
Security researchers and technology companies have also described a growing cybercrime marketplace that makes attacks easier to run. Criminals can now buy or rent phishing tools, scam infrastructure and stolen credentials much the way a legitimate business buys software services. That lowers the barrier to entry and helps small fraud operations scale quickly.
## Why text messages have become a favorite tool
Text scams have become one of the clearest examples of this shift. Messages arrive fast, feel personal and are often opened within minutes. In 2024, the Federal Trade Commission found that the share of text scam reports involving money loss rose to 11%, up from 9% in 2023 and much higher than in earlier years.
The most common themes are simple and familiar. Fake package delivery problems remain widespread. So do bogus unpaid toll notices. Officials have also warned about text messages claiming overdue traffic tickets, fake job offers and messages from impostors pretending to be a boss or a trusted institution.
These scams work because they create pressure. Many warn that a fee must be paid immediately or that access, delivery or driving privileges could be affected. The goal is not to hack a system in the classic sense. It is to make a person act before stopping to verify the message.
Security teams have observed how quickly these campaigns adapt. Phishing kits can now copy the look of real brands and agencies almost instantly, and scammers rotate websites and wording at high speed. In some cases, the same groups run package scams in one region and toll scams in another on the same day.

Even with all the newer tools, many attacks still come back to one thing: getting valid login details. Once criminals gain a real password, they may not need to break in at all. They can simply sign in.
That is one reason phishing remains so important. The national cybersecurity agency says phishing messages can arrive by email, text, direct message or phone call, usually by pretending to come from a trusted source. The message may ask for account details, payment information or a click on a malicious link.
Another growing problem is infostealer malware. These programs are designed to quietly harvest saved passwords, browser data, cookies and other credentials from infected devices. Recent industry reporting has pointed to infostealers as a major feeder system for wider cybercrime, because stolen logins can be used for bank fraud, shopping account abuse, workplace intrusions and identity theft.
## Defenses are changing too
The good news is that some of the best protections are becoming easier to use. Security guidance now puts more emphasis on phishing-resistant sign-in methods such as passkeys and stronger forms of multi-factor authentication. NIST has said phishing-resistant MFA is the best defense against these attacks because it reduces the chance that a stolen password alone can unlock an account.
Phone and messaging platforms are also adding more scam warnings, especially around suspicious links and impersonation attempts. Those tools help, but they do not remove the basic need for caution.
For consumers, the most reliable advice remains simple. Slow down when a message demands urgent action. Do not click links in unexpected texts or emails. Contact a company, toll operator, bank or delivery service using contact details you already know are real. Review account security settings. Use unique passwords or a password manager. Turn on strong MFA wherever possible.
The story of modern cyber risk is no longer only about giant breaches making headlines. It is also about quiet, constant pressure on ordinary people. The most common attack today may not look like a Hollywood-style hack. It may look like a normal message on an ordinary afternoon.
AI Perspective
This shift matters because it turns cybersecurity into a daily life issue, not just a corporate one. People are now being targeted through routine moments that feel harmless and familiar. The safest habit may be the simplest one: pause before you click, pay or sign in.


















































-b9c5792e.jpeg)










-dce9c62e.jpeg)

-e1b592cb.jpeg)
-ce4b953e.jpeg)
-40207ced.jpeg)
-30dcc245.jpeg)
-b7862b07.jpeg)
-c42917e1.jpeg)
-60308cea.jpeg)
-15a4fa8d.jpeg)
-standard-001-291bacf7.jpeg)
-f87b6017.jpeg)
-6670caec.jpeg)
-e3c107f2.jpeg)