[[[SUMMARY_START]]]
Cyber threats are changing quickly as attackers use stolen identities, software flaws and third-party access to break into corporate systems. Many companies are still struggling with basic defenses such as patching, authentication and supply-chain oversight. New data suggests the gap is widening as AI helps attackers work faster and at larger scale.
[[[SUMMARY_END]]]
Cybersecurity teams are facing a harder job in 2026. Attackers are not just finding new ways into company systems. They are also moving faster, using automation and AI tools to scan for weaknesses, steal credentials and exploit trusted suppliers. For many businesses, especially smaller ones and firms with complex digital operations, the pace of the threat is outstripping the pace of defense.
## A faster and more crowded threat landscapeRecent industry and public-sector findings point to the same problem: the cyber threat environment is speeding up. Attackers are leaning heavily on familiar methods, but they are using them with greater scale and speed.
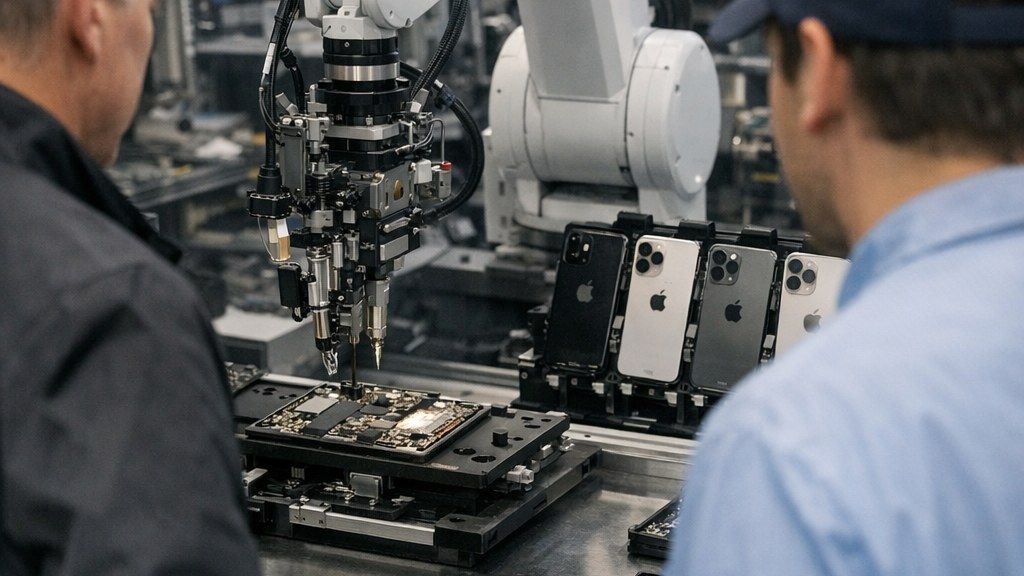
One major shift is the growing use of exposed software weaknesses. New research published in early 2026 found that attacks beginning with the exploitation of public-facing applications rose sharply, while vulnerability exploitation became the leading cause of incidents observed by one large security provider in 2025. At the same time, large supply-chain and third-party compromises have climbed steeply over the past several years.
That matters because many companies now depend on long chains of software vendors, cloud providers and outside services. A single weak link can open a path into a much larger target. In practical terms, a business may secure its own network reasonably well but still be exposed through a file-transfer tool, a software update process or a connected SaaS platform.
## Old problems still drive many breaches
The most striking finding is that many attacks still begin with basic failures. Stolen usernames and passwords remain one of the most common ways into company systems. Security researchers have also documented a booming market for stolen credentials, fueled by phishing and infostealer malware.
Breach data from 2025 showed that credential abuse and vulnerability exploitation were the two leading initial access paths. Third-party involvement in breaches also doubled to 30% in one major annual review, showing how often attackers now use partners, suppliers or service providers as a shortcut.
Ransomware remains a serious threat as well, even if executive attention is broadening toward fraud and phishing. In smaller organizations, the burden can be especially severe because they often have fewer security staff, older systems and less room for downtime. A ransom demand, data theft event or major outage can quickly become a business crisis.
## AI is speeding up attack work
Artificial intelligence is becoming an important force on both sides of cybersecurity, but defenders are warning that attackers are already using it to save time. Security analysts say AI tools can help threat actors research targets, sort large data sets, automate parts of reconnaissance and refine attack paths more quickly.

Business leaders are noticing the shift. A global outlook published in January 2026 found that AI-related vulnerabilities rose faster than any other category in 2025, and that many organizations expect AI to be the biggest force shaping cybersecurity this year. The same outlook found that cyber-enabled fraud has become a top concern for many executives.
## Why companies are struggling to keep up
Part of the challenge is structural. Many organizations are managing hybrid systems spread across on-premises networks, cloud platforms, remote devices and outside vendors. Every new connection can improve productivity, but it can also expand the attack surface.
Another problem is that strong cybersecurity still depends on disciplined routine work. Systems must be patched quickly. Access must be tightly controlled. Multi-factor authentication must be enforced. Backups must be tested. Suppliers must be assessed. Those tasks are not new, but they are hard to execute consistently across large and fast-moving organizations.
Public guidance continues to stress these basics. Federal agencies in the United States have urged companies to isolate backups, scan for vulnerabilities, bring senior leaders into cyber-risk decisions and push software makers toward more secure design practices. Updated standards such as the NIST Cybersecurity Framework 2.0 also put more emphasis on governance, making clear that cyber risk is not only an IT issue but a business issue.
## The likely direction from here
The broad picture is clear. The threat is not defined only by novel malware or dramatic hacks. It is increasingly defined by speed, scale and the growing ability of attackers to combine ordinary weaknesses into effective campaigns.
For companies, that means the gap may widen unless core security practices improve. The firms most likely to cope well are not necessarily those chasing every new tool. They are often the ones that can reduce complexity, secure identities, limit third-party exposure and respond quickly when something goes wrong.
AI Perspective
The main lesson is simple: cyber risk is becoming a speed problem as much as a technology problem. Many attacks still rely on basic weaknesses, but they now spread faster across more connected systems. Companies that treat security as a daily business discipline, not a side function, are more likely to keep pace.

























































-b9c5792e.jpeg)










-dce9c62e.jpeg)

-e1b592cb.jpeg)
-ce4b953e.jpeg)
-40207ced.jpeg)
-30dcc245.jpeg)